TL;DR
I did the exam on April 7th and captured all the flags achieving 100 points in 13h (10h30m if I discount the breaks). The next day, I delivered my report at around 20:00 and on the 9th I got the confirmation email that I had passed the exam 😉
Background
Ever since I started my professional life, I've been mostly a Systems Administrator. I've done some programming along the way too - still do, on personal projects, though not professionally anymore.
I've been doing pentesting professionally for around 5 years, two of them as a full-time job, but I'd been orbiting infosec way before that. I've done bug reporting (reporting issues I stumbled onto, not chasing bounties) and HTB (HackTheBox) mostly as a hobby dating well before that.
So, I was no stranger to what the OSCP wants from its students and what the objectives are. Nevertheless, I took it as a challenge to myself to get my first certification in infosec and a way to prove myself to that I was worthy.
Why OSCP in 2026
Well, to be honest, I needed the certification. Some clients require it, even though we (as a team) had the technical knowledge, we lacked the certification.
I actually started the certification in October 2025, and tried to get the exam done at the end of January, but some more important stuff came up which I couldn't push back, so I had to delay the exam to this month.
The Lab & PEN-200 Material
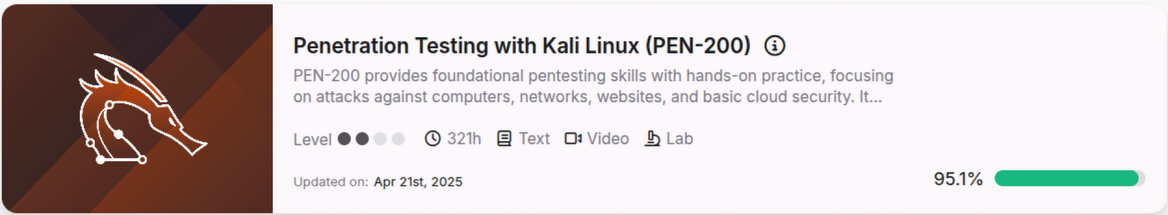
So, starting the PEN-200 course, I pretty much grinded all the modules from the syllabus in one and a half months, so by mid November I'd finished the theoretical part. I'm more of a hands-on guy, so I skipped the videos and just did the exercises.
At this time I took maybe a 3 week break from the course, due to work. Starting December, I got back to it full throttle and did all the Labs from the course until first week of January. All I was missing was more hands-on experience.
That's when I started doing the now famous TjNull's and LainKusanagi's lists. For reference, the boxes I did were the ones listed as "Proving Grounds Play" from both lists, "Proving Grounds Practice" from Lain's list, and the HTB's Windows and AD boxes from the Hack the Box section of Lain's list. All in all, I did around 110 boxes. 🙈
Most of the boxes I did were good practice and helped develop my personal methodology on how to approach the problems: what you know, what you don't know, but more importantly, how to correlate both! One of the most important things to learn is what you're missing to exploit something, and how to get it. Say you've got a box with two services: one has a remote file read, the other has an authenticated RCE. Odds are you need the first to feed the second. That's the kind of mental wiring you're trying to build.
If you're looking for calibration, I'd compare my exam to HTB Easy boxes. And don't glance at the "Community Rating" of Proving Grounds machines and think "I can never do this" because it's rated Very Hard — I think the community ratings are overrated, and OffSec's own ratings are much more in line with what the machines actually are.
Tooling & Notes
For note taking I use Obsidian, not because of any specific feature, but because that's what I'm used to. It's what I've used for ages and what I feel comfortable with.
I built my notes as I was doing the theoretical part of the course. By the time I finished, I had maybe 80% of the notes done. Doing boxes helped me finish the notes with more practical commands. For example, you can get the processes running on a Windows machine using PowerShell with Get-Process. But a more meaninful output could be obtained with
Get-CimInstance Win32_Process | Select-Object ProcessId, Name, @{Name="UserName";Expression={(Get-WmiObject -Class Win32_Process -Filter "ProcessId = '$($_.ProcessId)'").GetOwner().User}}, CommandLine | Format-Table -AutoSize
This gives you the process owner and full command line, which tells you immediately what's running as SYSTEM and with what arguments.
Get into the habit of keeping a list of go-to commands that work almost anywhere, and refining that list as you go, either for Windows or Linux.
One other thing I did was set up small scripts that help me save time. I had a script that I could use to start a reverse shell on windows (Start-RevShell.ps1) that downloaded nc.exe and started a reverse shell to my penelope instance. I had a script that would read the Recycle Bins of all users on the system (useful when you get local Administrator on a box). Good stuff for enumeration that can save you time collecting information manually.
The most important thing to understand is: do your own notes. You need to feel comfortable with them and know where the information is. My notes are useless to you because my way of thinking is different from yours.
Exam Day
As you should know by now, the exam comprises 6 machines: 3 of the AD set with an "assumed breached" scenario (where you already have credentials) and 3 individual boxes that can either be Windows or Linux. On my set, the individual boxes were two Windows and one Linux.
Every time I found a flag I took a 15/20 minute break to stretch my legs.
I started with the AD set because that's where I thought I would lose the most time (how I was wrong 🤐). I did all the basic Windows enumeration, in line with all the boxes and labs I'd done before and got the first flag at the 1h30 mark. Did my setup and configuration to reach the other two boxes on the set, and after some enumeration I found something interesting and was able to get the second flag (another 1h30). For the last flag I took another hour. All in all, it took me 4 and a half hours to fully compromise the AD set and I can say that there was nothing weird or really complicated about it. It all comes down to enumeration and connecting the dots.
After lunch, I started working on the individual machines and I totally skipped the first one. Didn't find anything on the first 20-30 minutes so I just skipped it.
The second one was pretty much the same, tried for 30 minutes and had nothing, skipped it.
Skipping early is a learned skill. Every minute you spend on a dead box is a minute you don't spend on a live one.
The third one had a fairly easy foothold which I was able to find quickly so I took my break here. When I came back, I kept going for 2 more hours until I got the final flag of the machine. This was around 18:45.
By that point I had 60 points. 70 to pass, so one flag away. I tried for another hour and a half on the remaining two boxes and got nowhere. Took a break for dinner.
Over dinner, something clicked. There was a tool I'd been ignoring in favour of doing the same thing manually, and I suddenly suspected that was exactly why I was stuck. After coffee with my wife I told her, "I think I know what I'm missing on at least one of those boxes." Went back to the exam and pwned it in 15 minutes.
80 points. I'd passed. Around 22:00.
I won't say what the tool was for obvious reasons, but the lesson generalizes: if you've got a tool that does a thing and you're doing the thing by hand, that's a smell.
The final box took me longer to figure out the foothold, but again, it was just something I was doing manually that I should have automated. Once I did that, in another 20 minutes I pwned that box too. And this was at 00:00.
Had a good night's sleep and first thing in the morning I rechecked all the flags making sure I had screenshots of everything I needed for the report and ended the exam with 1 hour to spare.
One thing to note is: the breaks worked wonders. Even if you're still thinking about the exam, you're not actually doing it. You're free to think whatever and try to come up with solutions to the doubts you have without the pressure of writing them on the terminal. Take your breaks!
Looking back, I never used a single exploit from searchsploit 😅.
Mistakes I Made
The last section already spoiled the big one, but it's worth saying out loud. My biggest mistake was not trusting the tools. If I had trusted them, I'd probably have cut 2 or 3 hours of dead time spent reading things that turned out to be nothing.
Looking back, there's another lesson worth calling out, and it might be the hardest one to internalize: sometimes what's missing is the clue. You've got a username but no password? Maybe you're supposed to brute-force it. searchsploit has nothing on that service? Maybe Google does. The absence isn't a dead end, it's the next step, pointing at what you should do instead. I learned this the hard way over 100+ labs and boxes.
Beyond those two, the prep paid off. The training had drilled it into me to not get stuck in rabbit holes, which saved me from the classic OSCP failure mode of sinking 4 hours into the wrong thing.
Resources I'd actually recommend
I want to emphasize the importance of actually working through all the modules in the course syllabus, especially if you're just starting. Even if you already know most of the material, going through it gives you a chance to build your notes in the same structure as the exam, which pays off later when you're grinding boxes.
A big shout-out to TJNull and LainKusanagi for their lists. The boxes on those lists cover the topics that actually matter for the exam, and grinding them is how you build a methodology that's fast enough to finish in 24 hours.
I'd also recommend SysReptor for the report. It's practically a no-brainer to just copy-paste from your notes straight into the report itself, and the default template helps you give structure to your thinking. Don't forget to save screenshots of web pages and RDP sessions, and save commands and their output as plain text in your notes, not as screenshots. It's much easier to Ctrl+F through text than to hunt through a screenshot gallery (and has the added bonus of syntax highlight on the report).
Then there's the obvious stuff that you should already have bookmarked: PayloadsAllTheThings, GTFOBins and HackTricks.
Would I do it again?
Well, totally!
If you're a seasoned pentester who lacks certifications, do it. You'll always learn something by the end of it, either a new method or a new way to organize your thoughts.
If you already have something like a CRTO or CRTP, just skip PEN-200 and go strait for PEN-300.
If you're just starting as a junior pentester, or want to start, do it. It has good content that relates to what you actually will find in the real world, but more importantly, it will build the methodology you need.
If you're looking for a career change and you have no background in systems administration or programming, honestly, this probably isn't for you yet. Start doing some HackTheBox machines and learn as you go. Don't expect to know everything there is to know after a week or two — there are concepts you need to understand before you can be successful in this field. Pentesting is more than finding an exploit with searchsploit and running it; you really need to understand what's working underneath, and how.
